For Installing Nessus on your machine:-
=> For installing Nessus on your machine or on kali there are many blog but this blog scope is to show you how to do full port scan so i have shared few blog link for installation of Nessus.
I Strongly recommend you to install Nessus on VM machine, but WHY ? At the end of this blog i explained.
Then to if you find any problem you can comment below, ill make separate blog for that :)
I Strongly recommend you to install Nessus on VM machine, but WHY ? At the end of this blog i explained.
Then to if you find any problem you can comment below, ill make separate blog for that :)
Full Port Scan using Nessus :-
=> Follow below configuration on your Nessus while doing FULL Port Scan :-
There are two GUI which nessus supports one is html and secound is flash you can use either of them as per your convenience
=> FLASH View
https://127.0.0.1:8834/flash.html#/
=> HTML View
https://127.0.0.1:8834/html5.html#/
I will be showing you full port scan by taking FLASH view .
There are two GUI which nessus supports one is html and secound is flash you can use either of them as per your convenience
=> FLASH View
https://127.0.0.1:8834/flash.html#/
=> HTML View
https://127.0.0.1:8834/html5.html#/
I will be showing you full port scan by taking FLASH view .
1) In Nessus Go to Policies and click on Add
2) General Setting :-
This step is critical step as you are doing full port scan setting here only
Name : Name of your scan
Visibility : Set it Private (you can set according to client requirement)
Under Port Scanner : Make sure Ping Host and TCP Scan should be unchecked
Under Port Scan Options : Give port Scan range 1-65535
3) Go to Credentials :-
Just skip this step as it is
4) Got to Plugins:-
Under Plugins make sure you disable Denail of Service.
Note: If client want to test their environment for DOS attack then you need to take permission from respective client then after you can perform this activity.
But i strongly recommend to disable this field while doing full port sacn.
5) Go to Preferences :
Just skip this step as it is and click on Submit button.
Note: While scanning any particular server OR any machine which is password set that time we use this feature where we specifically ask client to put the credentials of machine which we are scanning generally for configuration audit we use this feature
Now at this moment your Full port scan policy is configured .
Lets see how to scan ip address.
Step 1:- Click on Scans
Step 2 : Under Scans
Give the name , type of Scan which you are performing and policy which you just created
i.e
Name: Full port Scan
Type : There are 3 type under this, As we are doing full port scan so we will select Run Now.
you can select Scheduled or Template as required by you .
Policy : Select the policy which we just created
Step 3: Scanning Ip address
Put the IP address as shown below and then click on Launch Scan.
HAPPY SCANNING ..
Few TIPS and NOTES need to remember :-
1) TYPE OF IP ADDRESS
Below is few notes which you need to know before scanning ip address
Types of IP address :
Internal Scan :- you are scanning private ip address of the organisation
Private ip address include : 10.0.0.0/8, 172.16.0.0/12 and 192.168.0.0/16
External Scan:- you are scanning public ip address of the organization
Public IP address vs Private IP address
This step is critical step as you are doing full port scan setting here only
Name : Name of your scan
Visibility : Set it Private (you can set according to client requirement)
Under Port Scanner : Make sure Ping Host and TCP Scan should be unchecked
Under Port Scan Options : Give port Scan range 1-65535
Just skip this step as it is
4) Got to Plugins:-
Under Plugins make sure you disable Denail of Service.
Note: If client want to test their environment for DOS attack then you need to take permission from respective client then after you can perform this activity.
But i strongly recommend to disable this field while doing full port sacn.
5) Go to Preferences :
Just skip this step as it is and click on Submit button.
Note: While scanning any particular server OR any machine which is password set that time we use this feature where we specifically ask client to put the credentials of machine which we are scanning generally for configuration audit we use this feature
Now at this moment your Full port scan policy is configured .
Lets see how to scan ip address.
Step 1:- Click on Scans
Step 2 : Under Scans
Give the name , type of Scan which you are performing and policy which you just created
i.e
Name: Full port Scan
Type : There are 3 type under this, As we are doing full port scan so we will select Run Now.
you can select Scheduled or Template as required by you .
Step 3: Scanning Ip address
Put the IP address as shown below and then click on Launch Scan.
HAPPY SCANNING ..
Few TIPS and NOTES need to remember :-
1) TYPE OF IP ADDRESS
Below is few notes which you need to know before scanning ip address
Types of IP address :
Internal Scan :- you are scanning private ip address of the organisation
Private ip address include : 10.0.0.0/8, 172.16.0.0/12 and 192.168.0.0/16
External Scan:- you are scanning public ip address of the organization
Public IP address vs Private IP address
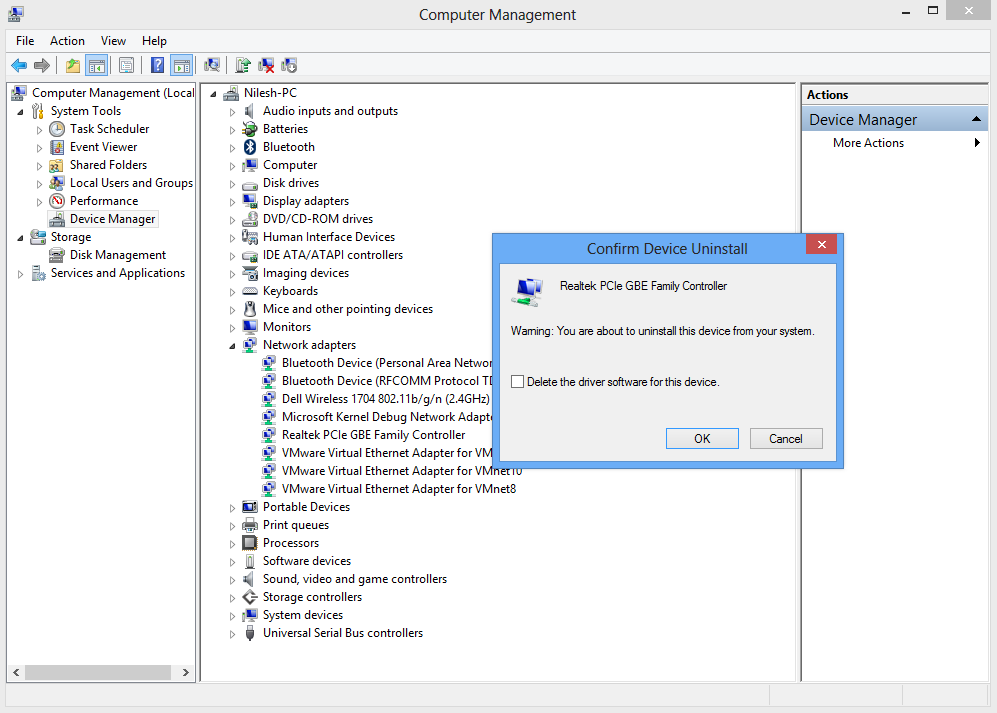
2) WHERE TO INSTALL NESSUS
I Strongly recommend you to install Nessus on VM machine loaded with Kali linux or backtrack
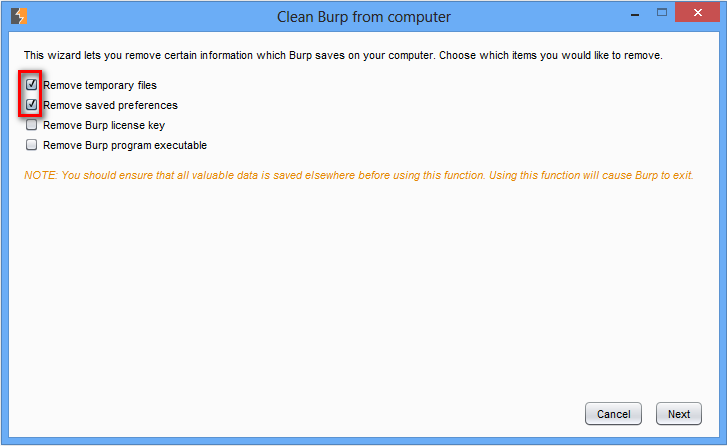
Reason 1 : If you are using Home feed version you can only scan 16 IP
Reason 2 : For scanning more than 16 IP either you need to uninstall nessus again or you require another mail id to generate new registration code
Now to solve above issue you can refer my blog how we use home feed version of nessus and scan more than 16 IP :)