Learn how to bypass Android SSL pinning using Frida and Objection runtime in this comprehensive blog. Explore the powerful combination of Frida's dynamic instrumentation and Objection's runtime manipulation to effectively bypass SSL pinning mechanisms in Android applications.
Identify if an Android application has SSL pinning enabled or not.
To verify if SSL pinning is enabled in an Android application, first, install the .apk file in the emulator by dragging and dropping it. Next, configure the Android emulator and Burp Suite for traffic interception.
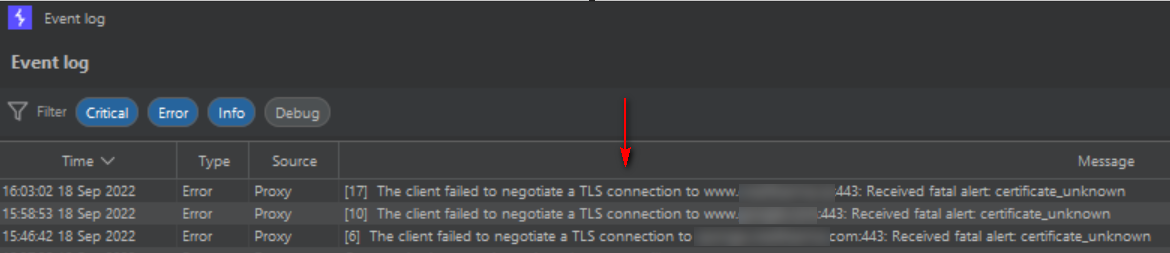
Launch the application on the emulator and navigate through its features. While testing, closely monitor Burp Suite's "Event log." If SSL pinning is active, the log will indicate its presence. Keep in mind that bypassing or disabling SSL pinning should only be done for legitimate testing purposes, as it may have security implications. Proceed with caution and follow ethical guidelines when attempting to bypass SSL pinning.
To circumvent SSL pinning or deactivate it, follow the steps below.
Start your emulator and make sure you are connected with adb devices
Step 1: Go to https://github.com/frida/frida/releases
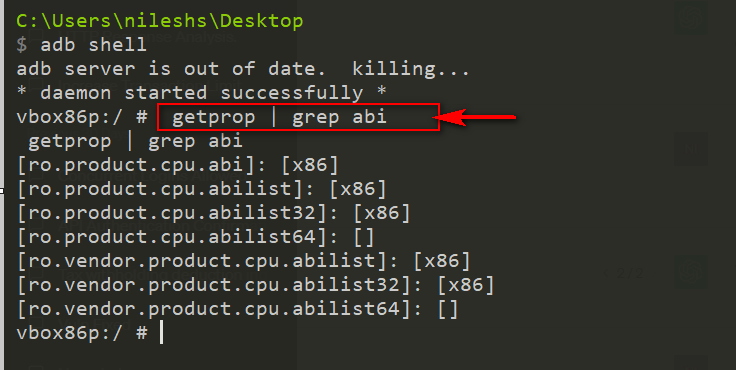
Step 2: Current dated latest release is - https://github.com/frida/frida/releases/tag/15.2.2 - from this search frida-server-15.2.2-android-x86.xz as per your environment. (to find your environment run below command)
The purpose of the command getprop | grep abi is to retrieve the Android Application Binary Interface (ABI) information on an Android device or emulator.
OR
Use the following command to get information about the CPU architecture:
adb shell getprop ro.product.cpu.abi
This command will return the architecture of the emulator, such as x86, x86_64, armeabi-v7a, or arm64-v8a.
Step 3: Download the file and paste it in your emulator directory as below
Commands:
- C:\Users\nileshs\Desktop\Android
- $ adb push frida-server /data/local/tmp/
Step 4:- Give the file permission to execute by command `chmod +x`
Commands for your reference:-
- C:\Users\nileshs\Desktop\Android
- $ adb shell
- vbox86p:/ # cd /data/local/tmp
- cd /data/local/tmp
- vbox86p:/data/local/tmp # ls
- ls
- frida-server
- vbox86p:/data/local/tmp # ls -ls
- ls -ls
- total 45308
- 45308 -rw-rw-rw- 1 root root 46387888 2022-09-18 02:56 frida-server
- vbox86p:/data/local/tmp # chmod +x frida-server
- chmod +x frida-server
- vbox86p:/data/local/tmp # ls -ls
- ls -ls
- total 45308
- 45308 -rwxrwxrwx 1 root root 46387888 2022-09-18 02:56 frida-server
Step 5:- Start frida server by command `./frida-server &`
Step 6:- Run Objection on the target application by below command
- C:\Users\nileshs>pip3 install objection
 |
- objection -g com.appname.mobile explore -q
- android sslpinning disable
- In your Genymotion emulator or mobile device, please ensure that all applications are closed. After running the command "objection -g com.appname.mobile explore -q," your targeted application should automatically open. This confirms that the objection is functioning correctly.
- If you encounter any errors related to the Frida server while running the objection command, please make sure to verify that your Frida server is running. Typically, such errors occur when the Frida server is stopped.
- Please execute the following command in the command prompt with administrator privileges.
- adb shell
- ps -e | grep frida-server
- kill -9 pid <pid of the frida-server>
Note:- In case you encounter any errors try to restart the Frida-Server